Written by
Mary Gonzalez, Director of Brand & Content
Published on
May 6, 2026
Updated on
May 6, 2026
Know Your Customer (KYC) requirements in telecom that began as loosely defined FCC anti-robocall mitigation efforts to protect consumers from fraud are quickly escalating beyond general guidance towards clearer enforceable KYC standards.
According to the FCC’s latest Draft Order, originating service providers (OSPs) must do more than collect customer information. They must be able to prove they know the business entities on their networks and are monitoring them over time. Most providers know they must “do KYC,” but few know what doing it correctly looks like in practice. Fewer still have the internal expertise, tools, or financial incentives to execute KYC in a way that holds up under regulatory scrutiny.
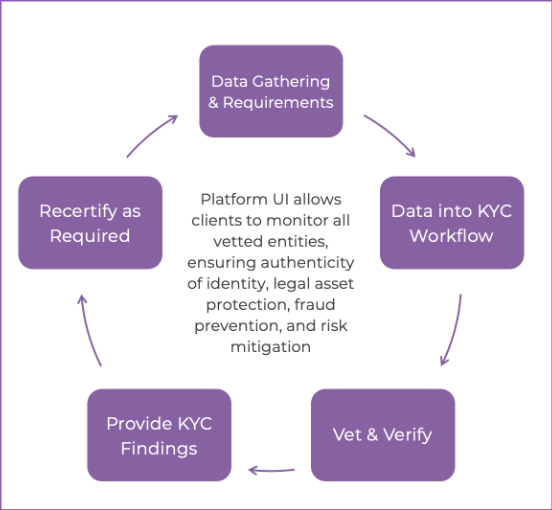
Numeracle’s KYC as a Service (KYCaaS) solution exists to close that gap, turning previously static, one-time checks into a continuously verified, defensible, auditable and scalable trust framework, without disrupting onboarding or revenue flow. Numeracle brings an operator’s view of KYC, with our expertise in rigorous identity vetting being shaped by daily exposure to real onboarding and verification workflows where new abuse tactics often surface.
This article is for OSPs, wholesale providers, VoIP operators, and CPaaS/CCaaS platforms preparing to tighten KYC practices while trying to keep business momentum. If you collect customer information once, store it, and hope it’s never questioned, this is where the risk starts to stack up.
Know Your Customer (KYC): Originating from the financial industry, when applied to communications, represents a framework for verifying the identity of an entity accessing a service or network.
Corporate KYC or Know Your Business (KYB): The application of KYC specifically to business entities.
For the purpose of this article, “KYC” will be used to encompass both KYC and KYB.
KYC operations must function reliably, consistently, and defensibly at every point in the customer lifecycle, whether during onboarding, growth, enforcement, or audit scenarios, without becoming an internal bottleneck.
[H3] Breakdowns & Gaps in Telecom “KYC” Today
When handled internally, KYC responsibilities are often distributed across various teams. Sales, legal, fraud departments, onboarding, and operations all interact with identity, but no single system or organization owns it end-to-end.
From what we’ve seen so far, fragmentation creates predictable risks:
When enforcement or traceback activity occurs, providers may know they “did KYC,” but cannot produce records showing what identity data was reviewed, what verification steps occurred, what risks were identified, or what rationale supported the decision to onboard and/or continue to retain a customer.
This is the gap where enforcement pressure lands.
Identity fraud and abuse evolves faster than service providers can realistically keep up with, as most internal vetting programs are built for static checks and slow change cycles.
Meanwhile, bad actors adapt quickly, using shell companies, layered ownership, short-lived domains, and manufactured business identities bolstered by AI designed to look just real enough to get through intake.
“If the solution to combat fraud is a guessing game, we are already losing to sophisticated targeted scams that are anything but guessing.”
— Rebekah Johnson, Founder & CEO (Numeracle); Identity Expert
For most service providers, maintaining the level of specialization to deal with changing abuse patterns internally is simply unrealistic. Numeracle’s extensive expertise on communications identity allows KYC practices to evolve continuously without adding staff, retraining cycles, or tool sprawl.
Numeracle's frontline exposure means we see how fraudulent actors attempt to bypass checks, including the rise of AI-generated businesses that appear legitimate on paper but lack real business liveness, every day. These insights are continuously folded back into verification standards, exceptions handling, and review logic, so our protections evolve and improve as abuse patterns change.
KYC as a Service is designed to fit into how providers already operate, while raising the bar behind the scenes.
Onboarding stays familiar to customers and internal teams. Providers initiate KYC through secure intake, and Numeracle handles the verification and review work using a blend of AI-automated correlation checks and policy-driven human review.
KYCaaS supports:
Numeracle is among the first solutions purpose-built to combat AI-generated fraud in telecom using AI itself, applying real-time learnings to detect non-live businesses that pass standard KYC checks.
As a result, KYC decisions are based on verified identity signals, not just what customers submit in a form. Intake data from an authorized representative is normalized and checked against external records to detect inconsistencies and early risk indicators before access is granted.
Operationally, this turns KYC into a standardized and repeatable workflow instead of a series of one-off judgements.
Real enterprises are complex. They operate in multiple jurisdictions, use brand names that differ from legal entity names, have intricate corporate structures, and change over time. These are normal conditions for legitimate business, not automatic red flags.
This is where many pass/fail KYC programs force false outcomes based on whether submitted information matches a narrow set of expected patterns and where fraudsters look for edge cases where partially valid information slips through.
KYCaaS is designed to escalate anomalies for deeper review rather than treating them as automatic failures or approvals. This may involve requesting supporting documentation, correlating additional sources, or performing targeted manual validation steps.
This approach does two things at once:
Good intent is not enough if business decisions cannot be shown later. In regulatory, traceback, or enforcement scenarios, providers are asked to demonstrate:
KYCaaS maintains structured records of KYC activity over time, allowing providers to respond with documentation rather than narrative explanations. This turns KYB from a memory-based process to one that is defensible on the record.
Business identity changes over time, and KYC must account for that reality.
After access is granted, KYCaaS continues to monitor identity attributes as data changes. Shifts in registration status, domain ownership, or related indicators can materially alter an entity’s risk profile.
Instead of relying on providers to periodically re-review customers manually, the platform alerts changes when they matter. This keeps KYB data current without adding operational burden.
Scaling networks is not the same as scaling identity operations. Using an expert third-party KYC vetting service allows providers to:
Now that KYC is showing up in real enforcement and traceback conversations, regulators are beginning to ask for more than collected data; they’re asking whether providers can show who the business was, how risk was evaluated at onboarding, and whether that identity was monitored over time.
For many providers, existing KYC processes were never built to answer those questions. They were built to get customers on the network, not to stand up months later under scrutiny, but that level of discipline is difficult to maintain alone.
Numeracle’s KYCaaS exists to make that possible without slowing onboarding or overloading internal teams. Our expertise comes from continuously operating KYC workflows in live telecom environments, which means our real-world learnings are applied directly back into our platform to strengthen verification rigor and documentation as fraud patterns change.
To see what operational KYC looks like in practice, visit www.numeracle.com/product/kycaas or contact Numeracle to discuss how KYCaaS fits into your business model.
Knowing your customers is no longer enough. Being able to provide it is what matters now.
Telecom service providers are expected to verify who their business customers are, assess risk before allowing traffic onto their network, and maintain enough documentation to show how those decisions were made.
This goes beyond collecting customer information and includes verification, monitoring, and the ability to demonstrate due diligence as regulators, state Attorneys General, or traceback groups inquire later.
OSPs prove KYC or KYB compliance by producing records that show what identity information was collected, how it was verified, what risks were identified, and why access was granted.
In practice, this means having a documented process and system of record that can show the provider knew at onboarding and whether identity was revisited as conditions changed.
The most effective way to implement KYB without slowing onboarding is to use a third-party KYC or KYB service designed for telecom. A managed approach like KYC as a Service (KYCaaS) allows providers to keep familiar onboarding flows while shifting verification, exception handling, documentation, and ongoing monitoring to a dedicated identity platform that scales with volume.